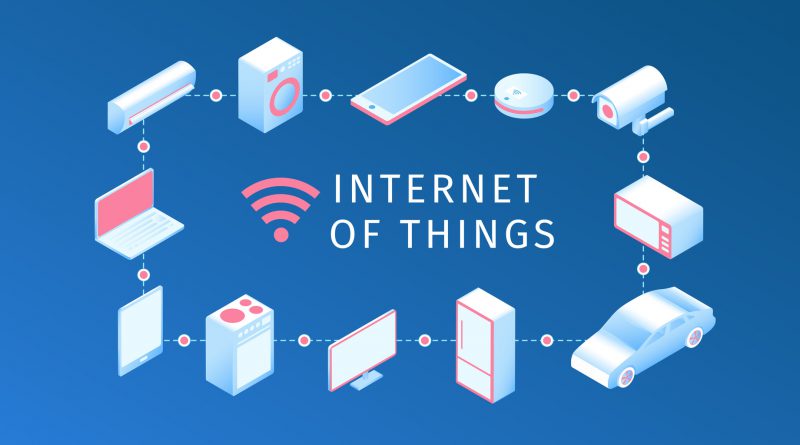
Malware exposure through Internet-connected devices an everyday thing
According to one tech expert, being exposed to malware originating from our use of Internet-connected devices is on its way to being – if not already – a common occurrence.
Rik Ferguson, Trend Micro’s global vice president for security research, spoke at the Info Sec conference in Dublin late last year. He said that the pervasive use of Internet-connected devices would most certainly result in less autonomous personal decision-making for the public, and exposure to ransomware and other malware attacks.
With smart technology being applied to household items such as TVs, fridges, and light bulbs and more, Ferguson stated this could possibly lead to malware attacks – especially if their security systems are left unattended.
“Much more needs to be done to make sure that these systems are protected. If you have a systems weakness in one area, that could lead to the infection of all the systems which you depend on,” he said.
There are many different avenues of attack, you have to think about them when thinking about the future.
Ferguson stated the problem should be addressed early in the development stages of the product. Ideally, smart tech products should not be released until security weaknesses are remedied. Companies should not be retrofitting solutions since this could compromise the whole network.
He also added “the spheres of bio tech and tech are not mutually exclusive. They overlap and as a result, when that technology does eventually blend, you will have people who try to compromise it,” adding that malware with the ability to infect people was “within the realms of possibility.”
The manufacturing industry should also undergo an upheaval similar to what the music industry went through in the early 2000s when they reconfigured due to the prevalence of downloading music through the Internet. Similarly, the dawn of 3D printing could the same effect on the manufacturing industry in the next decade or so.
As experts expect the number of Internet-connected devices to reach 20 billion by 2020, having sufficient security measures in place is imperative to be able to fight off cybercrimes.
Cloud-based services are one of the major entry points for cyberattacks, but cybercriminals look to other points of entry as well. Ferguson concluded, “There are going to be many different avenues of attack. You have to think on these avenues when you are thinking about the future.”
Comprehensive multi-device protection for you and your family for up to 6 PCs, Macs, Android, and iOS devices. For more info click here.