Hackers behind WannaCry Ransomware Committed Careless Mistakes
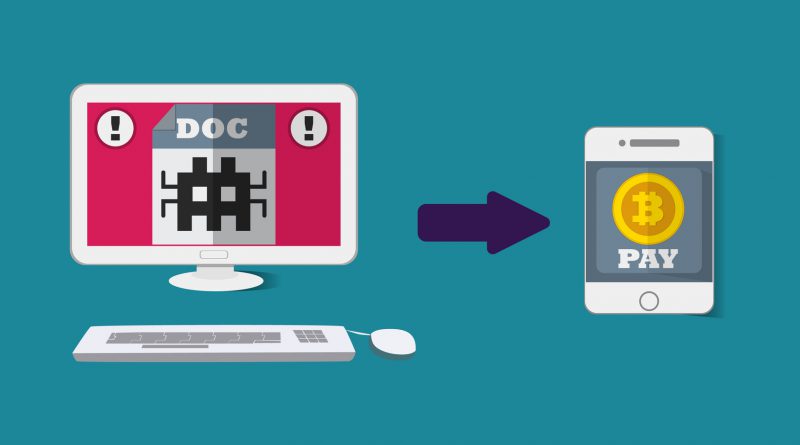
Over the past several days, WannaCry Ransomware swiftly developed into the worst online hacking to hit the Internet in recent years.
While the new ransomware strain was successful in halting a number of different services across Europe – affecting hospitals, telecom companies, and gas and electric providers, among others – industry experts were quick to label the hackers behind the malware as amateurs.
WannaCry was effective in terms of its reach, with over 200,000 devices in 150 countries victimised, but cybersecurity experts concluded that the process in creating the ransomware shortchanged the hackers’ potential profit and range.
As experts investigated the program, several missteps were discovered in the coding of WannaCry.
Among the mistakes found in the code of WannaCry was how the team created the program in a web-based “kill switch” that shortened its spread, misuse of the bitcoin payment process which made it easier to track their profits, and a wonky ransom function in their malware.
Experts also discovered WannaCry made it impossible for the hackers to know who among their victims have paid or not. Though the effects were truly severe in some parts of the world, analysts believe WannaCry could have been so much worse in the hands of more experienced cybercriminals.
By some estimates, the WannaCry team earned an estimated US $55,000 – a measly amount compared to some of the more successful multimillion dollar hauls some of the more professional hackers have made in the past.
Authorities deemed it a catastrophe as far as ransomware attacks go because it might have been one of the most damaging, far-reaching, and publicised of recent attacks, but it has barely anything to show for it money-wise.
The WannaCry hackers’ measly profits might have been a direct result of their malware not being able to fulfill its ransom function. As researchers looked through the code, they saw how it was not able to verify if a specific victim has sent their $300 bitcoin payment. Their code did not have the ability to identify the details of the payer, and in effect, it could not set the decryption process.
WannaCry was effective, reaching 200,000 computers in 150 countries, but experts still considered it amateurish.
The hackers were forced to figure out which computer to decrypt while the payments came in – an unenviable task considering the number of infected computers. This led to a more manual and grueling process for the hackers to undergo.
There have also been reports of victims not regaining access to their devices even after sending the ransom payment. Experts said that this proved how the hackers were not prepared to deal with this large of an outbreak.
Their bitcoin issues do not stop there, as having limited bitcoin addresses in their system makes it much easier for law enforcement and other authorities to track their moves. To make matters worse for the WannaCry team, these transactions are readily available on blockchain, bitcoin’s public ledger.
Researchers also said that WannaCry has some non-functional features. Its “check payment” button does not seem to verify if bitcoins have been received. It only gives answers at random – three fake error messages and another fake decryption message.
In addition, WannaCry’s faulty program broke the “trust model” that ransomware usually possess, giving no incentive for victims to pay up.
A number of cybersecurity experts have suspected that WannaCry might not have been a moneymaking scheme at all, as it caused so much chaos with little monetary benefits to show for it. They speculated that the hackers are trying to send a message to embarrass the NSA by applying their leaked hacking tools.
Some researchers have gotten behind the notion that the hackers were just trying to wreak as much havoc and cause as much destruction as possible. While the whole WannaCry epidemic could have been a lot worse, experts warn that the ransomware strain could attract imitators who are more skilled and more experienced compared to WannaCry’s agents – causing more damage and raking in more money.
Comprehensive multi-device protection for you and your family for up to 6 PCs, Macs, Android, and iOS devices. For more info click here.